Category: security
Coding and US Security
If you’re a history teacher, here’s a reprint of an article I wrote a few years ago. It’s a great tie-in to Hour of Code:
During WWI, the Choctaw language had been used to transmit U.S. military messages. With this thought in mind, Philip Johnston, the son of a missionary grew up on a Navajo reservation and spoke the Diné tongue fluently, brought the suggestion of a similar code to General Clayton Vogel early in 1942. The Diné language has no alphabet, uses no symbols and one sound may hold an entire concept. The idea was tested and proved to be faster and more reliable than the mechanized methods. The language has more verbs than nouns, that helps to move the sentences along and makes it far more difficult for outsiders to learn – making it the most ingenious and successful code in military history.
Share this:
Teacher-Authors: What’s Happening on my Writer’s Blog
A lot of teacher-authors read my WordDreams blog. In this monthly column, I share a popular post from the past month (or so).
***
 Tech Tips for Writers is an occasional post on overcoming Tech Dread. I’ll cover issues that friends, both real-time and virtual, have shared. Feel free to post a comment about a question you have. I’ll cover it in a future tip.
Tech Tips for Writers is an occasional post on overcoming Tech Dread. I’ll cover issues that friends, both real-time and virtual, have shared. Feel free to post a comment about a question you have. I’ll cover it in a future tip.
This tip is about visiting a website that gives you an error code similar to this:

You probably think the site isn’t working, but a lot of times, it’s a different easily solved problem that takes no time to do.
Look at the URL address (at the top of the webpage):

If it has https (like this one does), it could mean the website hasn’t been changed from http to https so it doesn’t recognize the address. All you have to do is delete the ‘s’ in the URL to make the site work:

I blurred everything out for privacy, but I think you can see I changed the https to http. The site immediately opened. Interestingly, that works over half the time.
If a site you manage has that problem, check with your host or IT folks and upgrade to https security protocol. Often, that’s free.
Jacqui Murray is the author of the popular Man vs. Nature saga, the Rowe-Delamagente thrillers, and the acclaimed Building a Midshipman, the story of her daughter’s journey from high school to United States Naval Academy. She is also the author/editor of over a hundred books on integrating tech into education, adjunct professor of technology in education, blog webmaster, an Amazon Vine Voice, and a freelance journalist on tech ed topics. Look for her next prehistoric fiction, Natural Selection, Summer 2022
Share this:
Is it Time for a Social Media Awareness Class?
Christian Miraglia, Ask a Tech Teacher contributor, has some great ideas on teaching kids about Social Media Awareness:
Over the last decade, there has been pressure in the K-12 learning environment to create classes that address everything from managing your money to various efforts to address cultural inequalities. The problem with including these classes, which all have good intentions, is that there is not enough time to address these subjects without taking away from core subjects. However, with the continued issue of social media’s influence on our teens, I think it is time to address this, especially in light of the recent massacre in Uvalde. The shooter was a user of Yubo and had posted threatening messages on the platform. I am sure that many teachers and parents have never heard of Yubo, which creates a problem in itself. Since the problem is complex, there are no simple solutions, but in light of what we see as educators, it is time to address the problem of social media use by our children in an educational setting.
Teachers understand the influence social media has had on students. In a recent article in the publication EdSurge, teacher Tyler Rablin lamented on losing battle with students’ cellphone use in schools. He conveyed his frustration with having students distracted by social media alerts and viewing videos as he tried to teach. I experienced the same in my years in the classroom. Whether it was text messages or videos, I encountered daily disruptions to my teaching, no matter what measure I took. Rabin’s solution was to ban cell phone usage. I applaud him in this endeavor, but I also think that students must be made formally aware of the influence of social media.
Share this:
June is Internet Safety Month
June is National Internet Safety Month, thanks to a resolution passed in 2005 by the U.S. Senate. The goal is to raise awareness about online safety for all, with a special focus on kids ranging from tots to teens. Children are just as connected to the Internet as adults. This is a great list of internet cautions I got from an online efriend a few years ago. I reprint it every year because it covers all the basics, avoids boring details, and gives kids (and adults) rules to live by:
Not everything you read online is true
It used to be anything we read in print was true. We could trust newspapers, magazines and books as reliable sources of information. It’s not the same with the web. Since anyone can become published, some of the stuff you’re reading online isn’t true. Even worse, some people are just rewriting stuff they read from other people online, so you might be reading the same false information over and over again. Even Wikipedia isn’t necessarily a reliable source. If you’re researching something online, consider the source. Some poorly written, random web page, isn’t necessarily a good source. However, if you find a .gov or .org site, the information has a better chance of being true. Always look at who owns the website and whether or not they have an agenda before considering whether or not certain information is true.
Not everyone you meet online are who they say they are
This is the hard part because we want to trust our friends, even our online friends. The truth is, some of the people you meet online are lying about who they really are. Sometimes adults pretend to be kids and kids pretend to be someone else. They do this for a variety of reasons; grownups might want to try and have sex with kids or frenemies might want to act like friends to get information on someone they want to bully at school or online. Unless you know someone very well and can verify their identity, don’t trust that everyone who you speak to online are who they say they are.
Some people who are pretending to be kids really aren’t. There are grownups who pretend to be kids so teens and kids won’t get creeped out talking with them. This is never a good thing. Most of the grownups who are looking to talk to kids are looking for sex. Parents need to monitor their kids’ friends list and ask questions about the friends they don’t know. It’s more prevalent than you think and it COULD happen to you.
Not everyone you “friend” is your friend. Just like in the real world, not everyone you know is a friend. Think long and hard about the people you’re “friending.” Drama doesn’t just stay in school anymore, now it follows you home thanks to the social networks. Plus, stuff y
ou share with what you think is a private social networking page is a simple cut and paste away from being broadcast all over school. Also, be careful when friending friends of friends and friends of friends of friends. You don’t really know these people, why are you giving them access to your private life? Sometimes, it’s like giving them the keys to your house.
Share this:
World Backup Day–March 31st
March 31st is called World Backup Day. At least once a year, backup your data files to an external drive (like a flash drive). This is one that isn’t connected to your local computer so can’t be compromised if you get a virus. It’s good to always backup data to cloud drives or a different drive on your computer but once a year, do the entire collection of data files to what is called an ‘air gap’ drive–one that is separated from any internet connection.
How to do this
There are various ways to back up your data. You can back up your data to an external device or a cloud-based backup service, or to both. You might even make more than one backup to external storage devices and keep the two copies in different places (providing protection and access to your data even if one of the backup devices is destroyed or inaccessible. Preserving your valuable documents and images for future access and use requires planning, as well as the use of automatic backup services.
To back up PC/Windows, use Windows Backup:
-
- Click the start button.
- Go to Control Panel
- Select ‘Backup and Restore’
- Select ‘Backup Now’
From there, select a drive with sufficient space and start. Be forewarned: If you have a lot of data, it takes a while. You can work on your computer while it’s backing up; it’ll just be slower.
Mac: Use the Time Machine tool.
Chromebook: No need. Everything is saved to the cloud. Now if you want to backup your cloud, use a service like Backupify.
Share this:
#1 Skill to Teach–Protect Student Privacy
I’ve written a lot about the importance of teaching students to protect their online privacy. Yes, we must do what we can on the campus but the real impact will come from students taking care of themselves. District Administration has a great article on this topic. See what you think:
9 ways school leaders can protect privacy while protecting kids online
Matt Zalaznick
 Monitoring is not quite the right word to describe the responsibility educators have when thinking about students’ online activity outside of school hours, a cyberbullying expert says.
Monitoring is not quite the right word to describe the responsibility educators have when thinking about students’ online activity outside of school hours, a cyberbullying expert says.
Ask a Tech Teacher has several articles you will enjoy on this same topic:
How to Teach Social Media Safety
6 Ways Teacher-authors Protect Their Online Privacy
5 (free) Security Posters for Tech Ed
Share this:
6 Ways Teacher-authors Protect Their Online Privacy
 If we humans aren’t giving away our personal information (as we do on FB, Tiktok, Instagram, Twitter and every other social media account), we’re having it stolen without our permission or knowledge and sold to those who mean us harm. As a teacher-author, this is a bigger deal than most because:
If we humans aren’t giving away our personal information (as we do on FB, Tiktok, Instagram, Twitter and every other social media account), we’re having it stolen without our permission or knowledge and sold to those who mean us harm. As a teacher-author, this is a bigger deal than most because:
- we have copyrighted files that provide us an income.
- we have a access to our income streams on our digital devices. If we’re hacked, the bad guy can shut us out of those and divert the monies from them to himself.
Because of this, I spend more time than most Normal People I know trying to secure my online environment. Here are six easy steps everyone should implement. To keep this article as short as possible, I don’t go into a lot of detail, simply an explanation of what the security feature is, why I use it, and what’s involved initiating it on your device:
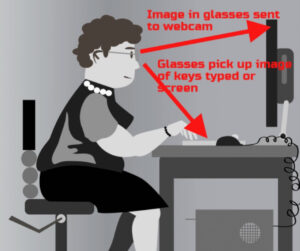
Cover your webcam
Any moderately-talented hacker can access your computer’s webcam and microphone remotely. Lots of movies and novel spotlight this invasion of privacy because it has been normalized in the digital world. You can make this invasion difficult for Bad Guys by covering your webcam, either with a sock or a post-in note. And, if your digital device of choice is a laptop, when you finish, close it. Don’t leave it sitting open with a view of your bedroom, your face, and a reflection of your keystrokes in your glasses.
VPN
A VPN (Virtual Private Network) hides (masks) your real location (your IP address) from prying eyes by bouncing it around to other parts of the world. For me, this week, it’s Australia. Other weeks, it’s Britain. These involve a monthly charge, probably a download, and minimal setup. VPNs can be used on phones, desktops, laptops, iPads, and more.
The setup for my chosen VPN (Surfshark) wasn’t difficult but it is a bit quirky when compared to my norm so it takes some getting used to (for example, Outlook won’t send email through a VPN so I have to turn it off first).
Share this:
Tech Tip #44: Computer Safety
 In these 169 tech-centric situations, you get an overview of pedagogy—the tech topics most important to your teaching—as well as practical strategies to address most classroom tech situations, how to scaffold these to learning, and where they provide the subtext to daily tech-infused education.
In these 169 tech-centric situations, you get an overview of pedagogy—the tech topics most important to your teaching—as well as practical strategies to address most classroom tech situations, how to scaffold these to learning, and where they provide the subtext to daily tech-infused education.
Today’s tip: Computer safety
Category: Maintenance, Security
Q: I’m afraid of getting slammed with viruses, malware–all that bad stuff that comes with visiting the internet. What do I do?
A: If you take reasonable precautions, the chances of being hit are minimized. Here are two first-steps:
- Don’t download from music or video sites. They carry the greatest danger of malware statistically.
- Make sure your firewall is working.
Sign up for a new tip each week or buy the entire 169 Real-world Ways to Put Tech into Your Classroom.
What’s your favorite tech tip in your classroom? Share it in the comments below.
Share this:
World Password Day — It’s Today!
One of the most important yet underwhelming international events is coming up the first Thursday in May (in Canada, it’s March 15th). What is it? It’s World Password Day,
Yawn…
I know — words can’t express how tedious most people find passwords, how annoying they are to use, and how likely it is 99% of the world will not celebrate this event. Let me see if I can convince you otherwise. On January 1, 1983, when the Internet was invented, mankind agreed to a binary choice: Invent passwords or forever regret their absence. Without them, there would be no protection for your privacy, your online information, or even your personal identity. Passwords are now required to access websites, banking, email, social media, favorite shopping sites, chat venues like iMessenger, and even certain documents. These annoying, forgettable, intrusive entities are the first line of defense against hackers and for many, their entire defense. Because so many treat passwords casually, despite all they know about their importance, password theft is one of the fastest growing and most effective crimes.
While every expert recommends changing your password two-three times a year, no one does that. Do you? I don’t. I’m challenged to remember my password much less remember to change it regularly. As a result, World Password Day came into being:
Annually, on World Password Day, change all of your passwords
Share this:
5 (free) Security Posters for Tech Ed
Every month, we’ll share five themed posters that you can share on your website (with attribution), post on your walls, or simply be inspired.
This month: Security
–for the entire collection of 65 posters, click here
Jacqui Murray has been teaching K-18 technology for 30 years. She is the editor/author of over a hundred tech ed resources including a K-12 technology curriculum, K-8 keyboard curriculum, K-8 Digital Citizenship curriculum. She is an adjunct professor in tech ed, Master Teacher, webmaster for four blogs, an Amazon Vine Voice, CSTA presentation reviewer, freelance journalist on tech ed topics, contributor to NEA Today, and author of the tech thrillers, To Hunt a Sub and Twenty-four Days. You can find her resources at Structured Learning.