Jacqui Murray has been teaching K-18 technology for 30 years. She is the editor/author of over a hundred tech ed resources including a K-12 technology curriculum, K-8 keyboard curriculum, K-8 Digital Citizenship curriculum. She is an adjunct professor in tech ed, Master Teacher, webmaster for four blogs, an Amazon Vine Voice, CSTA presentation reviewer, freelance journalist on tech ed topics, and author of the tech thrillers, To Hunt a Sub and Twenty-four Days. You can find her resources at Structured Learning.
Tag: security
June is Internet Safety Month
June is National Internet Safety Month, thanks to a resolution passed in 2005 by the U.S. Senate. The goal is to raise awareness about online safety for all, with a special focus on kids ranging from tots to teens.
Here’s a short list of internet cautions I got from online efriends. I reprint it every year because it covers all the basics, avoids boring details, and gives kids (and adults) rules to live by:
Not everything you read online is true
It used to be anything we read in print was true. We could trust newspapers, magazines and books as reliable sources of information. It’s not the same with the web. Since anyone can become published, some of the stuff you’re reading online isn’t true. Even worse, some people are just rewriting stuff they read from other people online, so you might be reading the same false information over and over again. Even Wikipedia isn’t necessarily a reliable source. If you’re researching something online, consider the source. Some poorly written, random web page, isn’t necessarily a good source. However, if you find a .gov or .org site, the information has a better chance of being true. Always look at who owns the website and whether or not they have an agenda before considering whether or not certain information is true.
Share this:
June is Internet Safety Month
June is National Internet Safety Month, thanks to a resolution passed in 2005 by the U.S. Senate. The goal is to raise awareness about online safety for all, with a special focus on kids ranging from tots to teens.
Here’s a short list of internet cautions I got from an online efriend a few years ago. I reprint it every year because it covers all the basics, avoids boring details, and gives kids (and adults) rules to live by:
Not everything you read online is true
It used to be anything we read in print was true. We could trust newspapers, magazines and books as reliable sources of information. It’s not the same with the web. Since anyone can become published, some of the stuff you’re reading online isn’t true. Even worse, some people are just rewriting stuff they read from other people online, so you might be reading the same false information over and over again. Even Wikipedia isn’t necessarily a reliable source. If you’re researching something online, consider the source. Some poorly written, random web page, isn’t necessarily a good source. However, if you find a .gov or .org site, the information has a better chance of being true. Always look at who owns the website and whether or not they have an agenda before considering whether or not certain information is true.
Share this:
Happy New Year! And Public Domain Day
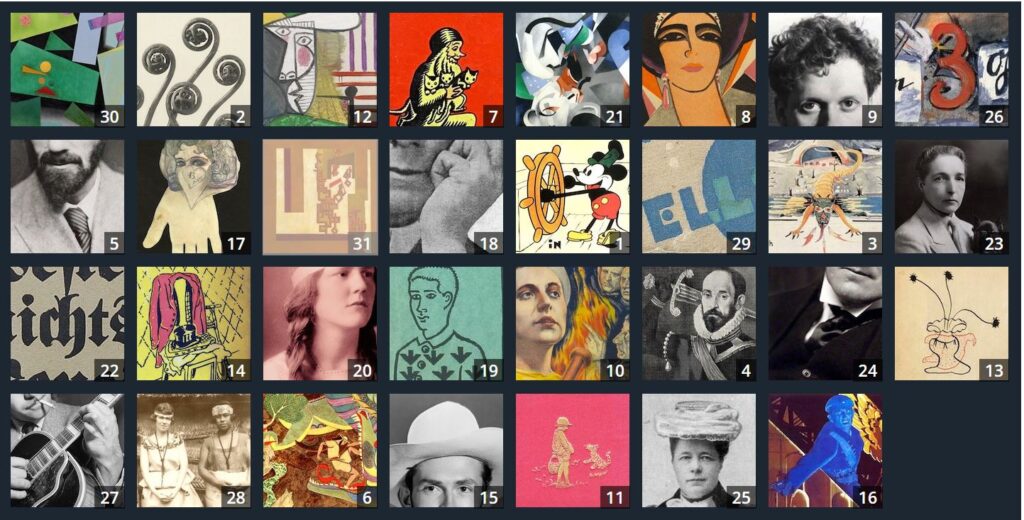
Also on January 1st: It’s Public Domain Day! Every year, January 1st is Public Domain Day. This is an observance of when copyrights expire and works enter into the public domain–free for all to use. According to Public Domain Review, here are some of the newly-available artistic works you might like a/o January 1, 2025:
The picture above is interactive on the website. If you click it, you enter Public Domain Review’s website and can then explore each of these new sources of inspiration, free to use.
A few recently released that caught my attention:
[gallery type="slideshow" size="large" ids="70637,70639,70638,70632,70631,70635,70636,70634,70633"]Here’s the sign-up link if the image above doesn’t work:
https://forms.aweber.com/form/07/1910174607.htm
“The content presented in this blog are the result of creative imagination and not intended for use, reproduction, or incorporation into any artificial intelligence training or machine learning systems without prior written consent from the author.”
Jacqui Murray has been teaching K-18 technology for 30 years. She is the editor/author of over a hundred tech ed resources including a K-12 technology curriculum, K-8 keyboard curriculum, K-8 Digital Citizenship curriculum. She is an adjunct professor in tech ed, Master Teacher, freelance journalist on tech ed topics, and author of the tech thrillers, To Hunt a Sub and Twenty-four Days. You can find her resources at Structured Learning.
Share this:
13 AI Detectors and 11 Plagiarism Detectors
Here are popular online resources to teach about AI detection and Plagiarism detection:
AI Detector
Click here for updates to this list:
- AI Content Detector–from Crossplag
- AI Text Classifier–from the creators of ChatGPT to identify writing from an AI
- ChatGPT–has developed their own tool to find AI-generated writing
- Content at Scale AI Content Detector
- Contentdetector.org
- Copyleaks AI Content Detector
- Crossplag–detect AI content
- GPTZero–to find text generated by an AI
- Plagiarismchecker.ai
- TurnItIn ithenticate–new tool to identify AI-generated text
- UNDETECTABLE.AI
- Winston A.I
- ZeroGPT
Finding plagiarism
Share this:
June is Internet Safety Month
June is National Internet Safety Month, thanks to a resolution passed in 2005 by the U.S. Senate. The goal is to raise awareness about online safety for all, with a special focus on kids ranging from tots to teens.
Here’s a short list of internet cautions I got from an online efriend a few years ago. I reprint it every year because it covers all the basics, avoids boring details, and gives kids (and adults) rules to live by:
Not everything you read online is true
It used to be anything we read in print was true. We could trust newspapers, magazines and books as reliable sources of information. It’s not the same with the web. Since anyone can become published, some of the stuff you’re reading online isn’t true. Even worse, some people are just rewriting stuff they read from other people online, so you might be reading the same false information over and over again. Even Wikipedia isn’t necessarily a reliable source. If you’re researching something online, consider the source. Some poorly written, random web page, isn’t necessarily a good source. However, if you find a .gov or .org site, the information has a better chance of being true. Always look at who owns the website and whether or not they have an agenda before considering whether or not certain information is true.
Share this:
Happy New Year! And Public Domain Day
Also on January 1st: It’s Public Domain Day! Every year, January 1st is Public Domain Day. This is an observance of when copyrights expire and works enter into the public domain–free for all to use. According to Public Domain Review, here are some of the newly-available artistic works you might like a/o January 1, 2024:
The picture above is interactive on the website. If you click it, you enter Public Domain Review’s website and can then explore each of these new sources of inspiration, free to use.
The big excitement this year that has everyone talking is Walt Disney’s original designs for Steamboat Willie–the precursor to Mickey Mouse. As of January 1st, it is available to all. Some history from Wikipedia:
“It could have entered the public domain in four different years: first in 1955, renewed to 1986, then to 2003 by the Copyright Act of 1976, and then to 2023 by the Copyright Term Extension Act (also known pejoratively as the “Mickey Mouse Protection Act”) of 1998. It has been claimed that these extensions were a response by Congress to extensive lobbying by The Walt Disney Company.”
Here’s a 7-minute animation of Steamboat Willie from YouTube, with over 13 million views:
Here’s the sign-up link if the image above doesn’t work:
Jacqui Murray has been teaching K-18 technology for 30 years. She is the editor/author of over a hundred tech ed resources including a K-12 technology curriculum, K-8 keyboard curriculum, K-8 Digital Citizenship curriculum. She is an adjunct professor in tech ed, Master Teacher, webmaster for four blogs, an Amazon Vine Voice, CSTA presentation reviewer, freelance journalist on tech ed topics, contributor to NEA Today, and author of the tech thrillers, To Hunt a Sub and Twenty-four Days. You can find her resources at Structured Learning.
Share this:
How to Kidproof the Internet
How to keep children safe online is the most popular question parents ask at my school. They want to know about firewalls, filters, kidsafe desktops, nannycams, cyberbullying, internet privacy, and everything in between. Should they keep their children away from computers or just off the internet? Do they have to sit with them while they work? Is there an age when it’s OK to let them on their own?
No. No. and No. Parents must teach children to take care of themselves while visiting the vast, anonymous, addictive neighborhood called ‘the internet’. Just as they stay at your side in large busy stores, don’t talk to strangers, and don’t open the door to people they don’t know, they will learn to be safe in the digital world. Because it’s part of our genome–to do what keeps us safe.
While they’re getting to that epiphany, here are ideas you can employ to support them on the way:
- Teach your children to use the internet. They are digital citizens which includes rights and responsibilities they probably aren’t aware of. Just as in their neighborhood, they must learn them. Don’t hope school teaches them. They may, or might teach them wrong. Teach your kids to avoid ads, that anonymous isn’t innocent, and online relationships aren’t always friendly. Tell them again and again. Sooner than you think, they will own it. Just as they don’t cross the street without looking both ways, they won’t cross the ‘digital street’ unless it’s safe.
- Discuss what they can and cannot do online. Discuss why so they understand. You want them able to take care of themselves which means not putting themselves in harm’s way.
- Use a parental control filter. Block everything you worry about–chicks, Minecraft, girls, Facebook, xxx, murder. It’s easy to unblock if your child needs a site that won’t come up. More importantly, it leads to a conversation with your child about what they’re researching and why a particular site is relevant. You want your child comfortable with you involved in their lives–not as an arbiter of right and wrong, but an interested loving party.
- Do not assume parental controls are perfect. In fact, assume they aren’t. Stay vigilant. Be aware when your child is too quiet or too noisy at the computer. Ask questions. Pop in unexpectedly.
- Enforce rules. Don’t decide you’re too tired one night to go check a website your child tells you they need to visit. Always always always follow your own rules.
- Check ‘history’ on your child’s computer. Do it with them so they understand this is part of the plan to keep them safe.
- Know what their school does to keep your child safe online. Follow the same rules, or follow your own. Do explain the differences to your child. Children are flexible. They will be fine with varied rules.
Share this:
June is Internet Safety Month
June is National Internet Safety Month, thanks to a resolution passed in 2005 by the U.S. Senate. The goal is to raise awareness about online safety for all, with a special focus on kids ranging from tots to teens. Children are just as connected to the Internet as adults. This is a great list of internet cautions I got from an online efriend a few years ago. I reprint it every year because it covers all the basics, avoids boring details, and gives kids (and adults) rules to live by:
Not everything you read online is true
It used to be anything we read in print was true. We could trust newspapers, magazines and books as reliable sources of information. It’s not the same with the web. Since anyone can become published, some of the stuff you’re reading online isn’t true. Even worse, some people are just rewriting stuff they read from other people online, so you might be reading the same false information over and over again. Even Wikipedia isn’t necessarily a reliable source. If you’re researching something online, consider the source. Some poorly written, random web page, isn’t necessarily a good source. However, if you find a .gov or .org site, the information has a better chance of being true. Always look at who owns the website and whether or not they have an agenda before considering whether or not certain information is true.
Share this:
Teacher-Authors: What’s Happening on my Writer’s Blog
A lot of teacher-authors read my WordDreams blog. In this monthly column, I share the most popular post from the past month on my writer’s blog, WordDreams.
Here is one of the popular posts:
AI-generated art is a game-changer for writers who do their own marketing and newsletters. I was reminded of that when I received a newsletter from good blogger friend Luciana Cavallaro, author of amazing historical fiction centered in ancient Rome. She sent a newsletter and wanted to include an image of a coach being hit in the face by a volleyball (don’t ask–it’s complicated). As close as she could get was this image:
I accepted her challenge to find a better image and turned to DALL-E, one of the new platforms where AI generates art. Here’s what I got in about a minute:
This is new legal territory, but current thinking is that these images are free to use, owned by no one, similar to the legal permissions allowed by public domain images. Here’s an infogram explaining that, taken from DALL-E’s terms of service:
Share this:
World Backup Day–March 31st Every Year
March 31st is called World Backup Day. At least once a year, backup your data files to an external drive (like a flash drive). This is one that isn’t connected to your local computer so can’t be compromised if you get a virus. It’s good to always backup data to cloud drives or a different drive on your computer but once a year, do the entire collection of data files to what is called an ‘air gap’ drive–one that is separated from any internet connection.
How to do this
There are various ways to back up your data. You can back up your data to an external device or a cloud-based backup service, or to both. You might even make more than one backup to external storage devices and keep the two copies in different places (providing protection and access to your data even if one of the backup devices is destroyed or inaccessible. Preserving your valuable documents and images for future access and use requires planning, as well as the use of automatic backup services.
To back up PC/Windows, use Windows Backup:
- Click the start button.
- Go to Control Panel
- Select ‘Backup and Restore’
- Select ‘Backup Now’
From there, select a drive with sufficient space and start. Be forewarned: If you have a lot of data, it takes a while. You can work on your computer while it’s backing up; it’ll just be slower.
Mac: Use the Time Machine tool.
Chromebook: No need. Everything is saved to the cloud. Now if you want to backup your cloud, use a service like Backupify.